Fine-grained control over access to data spaces is important for maintaining confidentiality in any platform. Folder Controller Access Control (FCAC) provides a mechanism for defining these access restrictions at the directory level. This allows administrators to precisely control who can access, modify, and delete content within specific folders. FCAC integrates existing identity systems to ensure that only authorized users or groups have access to restricted information.
Controlled Access Pathways
Controlled access pathways are essential/critical/vital for maintaining/ensuring/guaranteeing the security/safety/integrity of a facility/system/area. These pathways are designed to regulate/restrict/monitor the flow/movement/access of personnel/individuals/users and vehicles/equipment/materials in and out of sensitive/restricted/protected zones. By implementing controlled/managed/regulated access points, organizations can minimize/reduce/prevent the risk of unauthorized/unlawful/inappropriate entry, theft, or damage/disruption/interference.
- Features of controlled access pathways include:
- Increased protection
- Reduced risk
- Improved accountability
Access to ANP Uploads
Securing your System Network Protocols (ANP) uploads is paramount. Implementing robust Authentication mechanisms ensures that only authorized Users can Post data. This involves Validating user identities, Setting granular Roles, and implementing Measures to prevent unauthorized Modification. A well-defined ANP upload Policy coupled with Ongoing monitoring is essential for maintaining the integrity and confidentiality of your uploaded data.
Detailed File System Access Control
In the realm of robust security architectures, fine-grained file system access control emerges as a cornerstone. This paradigm empowers administrators to meticulously define permissions at an intricate level, dictating which users or processes can interact with specific files or directories. By employing granular controls, organizations can mitigate unauthorized modifications, leaks, and potential breaches. Moreover, this approach fosters a secure environment where data integrity is preserved and confidentiality is maintained. Implementing fine-grained access control typically involves leveraging role-based permissions, attribute-based access control (ABAC), or policy engines that dynamically evaluate operations based on contextual factors.
Enforcing Data Security Through Access Control
Protecting sensitive information is paramount in today's digital landscape. Rigorous access control measures are essential to preserving data from unauthorized access, use, disclosure, disruption, modification, or destruction. By implementing granular access permissions, organizations can limit user access to specific resources based on their roles and responsibilities. This comprehensive approach helps to minimize the risk of data breaches and ensures compliance with relevant guidelines.
- Establishing a role-based access control (RBAC) system allows organizations to assign authorizations to different user roles, optimizing security management.
- MFA adds an extra layer of security by requiring users to provide multiple forms of verification before accessing sensitive data.
- Performing periodic reviews of user access rights helps to identify any potential vulnerabilities or unauthorized access attempts.
Implementing Robust Access Control Mechanisms
Securing sensitive information and regulating user access is paramount in today's digital landscape. Robust access control mechanisms panel de control de acceso ensure a crucial layer of protection by restricting access to resources based on predefined policies. A comprehensive approach involves deploying multiple safeguards, such as role-based access control (RBAC), multi-factor authentication (MFA), and perimeter security, to mitigate the risk of unauthorized access and data breaches. By defining granular permissions and enforcing strict authorization rules, organizations can protect their valuable assets and ensure compliance with relevant regulations.
 Yasmine Bleeth Then & Now!
Yasmine Bleeth Then & Now! Bug Hall Then & Now!
Bug Hall Then & Now!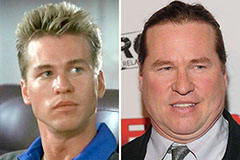 Val Kilmer Then & Now!
Val Kilmer Then & Now! Talia Balsam Then & Now!
Talia Balsam Then & Now! Heather Locklear Then & Now!
Heather Locklear Then & Now!